100% Valid Dumps For 70-680 Exam Pass: PassLeader have been updated the 580q 70-680 exam dumps and added the new exam questions, in the latest version of 70-680 PDF dumps or VCE dumps, you will get all the new changed 580q 70-680 exam questions, which will help you 100% passing 70-680 exam, and you will get the free version of VCE Player together with your 70-680 VCE dumps. Welcome to visit our website — passleader.com and get your 70-680 exam passed easily!
keywords: 70-680 exam,580q 70-680 exam dumps,580q 70-680 exam questions,70-680 pdf dumps,70-680 practice test,70-680 vce dumps,70-680 study guide,70-680 braindumps,TS: Windows 7, Configuring Exam
QUESTION 401
You need to prevent a custom application from connecting to the Internet. What should you do?
A. From Windows Firewall, add a program.
B. From Windows Defender, modify the Allowed items list.
C. From Windows Firewall with Advanced Security, create an inbound rule.
D. From Windows Firewall with Advanced Security, create an outbound rule.
Explanation:
Outbound Rule. Outbound rules allow you to block and allow traffic that originates on the computer from traveling out to the network.
Creating WFAS Rules. The process for configuring inbound rules and outbound rules is essentially the same: In the WFAS console, select the node that represents the type of rule that you want to create and then click New Rule. This opens the New Inbound (or Outbound) Rule Wizard. The first page, allows you to specify the type of rule that you are going to create. You can select between a program, port, predefined, or custom rule. The program and predefined rules are similar to what you can create using Windows Firewall. A custom rule allows you to configure a rule based on criteria not covered by any of the other options. You would create a custom rule if you wanted a rule that applied to a particular service rather than a program or port. You can also use a custom rule if you want to create a rule that involves both a specific program and a set of ports. For example, if you wanted to allow communication to a specific program on a certain port but not other ports, you would create a custom rule.
QUESTION 402
You have two computers named Computer1 and Computer2 that run Windows 7. You need to ensure that Computer2 has exactly the same firewall rules as Computer1. What should you do on Computer1?
A. Run Winrm.exe quickconfig.
B. From Windows Firewall with Advanced Security, select Export Policy.
C. From Windows Firewall with Advanced Security, click Inbound Rules and then click Export List.
D. Open Local Security Policy. Right-click IP Security Policies on Local Computer and then click Export List.
Answer: B
Explanation:
Importing and Exporting Firewall ConfigurationMost organizations that use clients running Windows 7 apply firewall rules through Group Policy. In the event that you need to support a number of stand-alone clients running Windows 7, you can replicate complex firewall configurations using the WFAS Import Policy and Export Policy options. Importing and exporting policy also allows you to save the current firewall configuration state before you make changes to it. Exported policy files use the .wfw extension. Exported policies use a binary format, not Extensible Markup Language (XML) format like many other Windows 7 configuration files. You can also export and import firewall policies in the same .wfw format using the netsh advfirewall export or netsh advfirewall import commands.
QUESTION 403
You have a computer that runs Windows 7. The network connection details are shown in the exhibit. (Click the Exhibit button.) You need to manually assign an IP address of 192.168.1.50 to the computer. What should you do first?
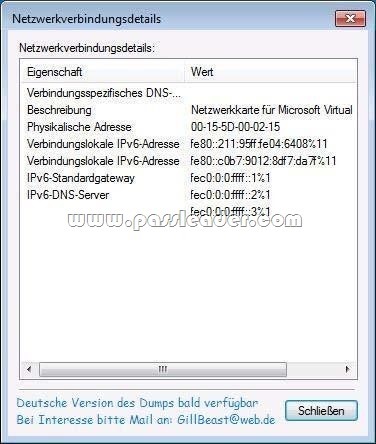
A. Enable TCP/IPv4.
B. Disable TCP/IPv6.
C. Run Ipconfig and specify the /renew parameter.
D. Run Netsh and specify the Interface ipv4 add address command.
Answer: A
Explanation:
IPv4 is not currently enabled and 192.168.1.50 is an IPv4 address.Therefore IPv4 is required so ENABLE it.
QUESTION 404
A network contains computers that run Windows 7 and Windows Vista. A computer named Computer1 runs Windows 7. You need to ensure that only users running Windows 7 and Windows Vista can connect to Computer1 using Remote Desktop. In the System Properties window, on the Remote tab, what should you do?
A. Click the Advanced button. Select the Allow this computer to be controlled remotely check box on Computer1.
B. Select the Allow connections only from computers running Remote Desktop with Network Level Authentication (more secure) check box on Computer1.
C. Select the Allow connections from computers running any version of Remote Desktop (less secure) check box on Computed.
D. Select the Allow Remote Assistance connections to this computer check box on Computer1.
Answer: B
QUESTION 405
You have a computer that runs Windows 7. You run the Configure Backup wizard as shown in the exhibit. (Click the Exhibit button.) 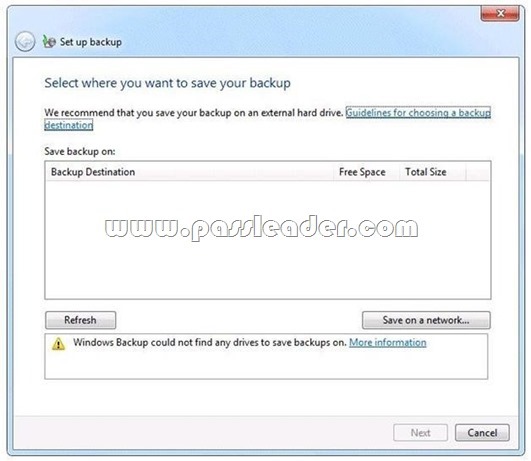
You need to ensure that you can back up the computer to a local disk drive. What should you do before you run the Configure Backup wizard?
A. Connect a removable disk.
B. Log on as an administrator.
C. Start the Volume Shadow Copy Service (VSS).
D. Add your user account to the Backup Operators group.
Answer: A
Explanation:
An external hard drive External hard drives can be removed and stored in a secure location. However, they are typically slower than internal hard drives and tend to be less reliable, mainly because they are by default formatted using FAT rather than NTFS. You cannot use an external hard drive for a System Image backup unless you convert its filing system to NTFS. Because it is easily removable, it is more likely that an external hard drive will be missing when a scheduled backup is required. (Local disk drive was specified, not internal)NOT AdministratorYou need administrator credentials to configure scheduled backups or to manually initiate a backup. However, restoring files does not require administrator privileges unless a user attempts to restore another user’s file. (NOTE: The issue was a lack of location to store the Backup, not being about to run the Configure Backup, thus it was assumed that the user in this scenario had administrator credentials)NOT Backup OperatorsMembers of this group are able to override file and folder access restrictions for the purpose of backing up data. You can allow a user to back up files and directories by assigning them to the Backup Operators group rather than by modifying the Back Up Files and Directories policy.NOT VSSVSS is installed on computers running Windows 7. Its startup type is Manual. The service starts as needed. If the service does not start when required, shadow copies are unavailable for backup and Windows Backup does not succeed. Nor can you create restore points and previous versions. In this case, check the service and ensure that it has not been disabled.
QUESTION 406
You use a computer that has Windows 7 SP1 installed. The computer has a shared folder named C:\Software. User1 is a local user account on the computer. The account is a member of several groups that have access to the C:\Software folder. You need to verify whether User1 can save files to C:\Software. What should you do?
A. Run the Net Share command.
B. Run the Wfs C:\Software command.
C. In the Advanced Security Settings for the Documents folder, select the Effective Permissions tab.
D. Run the Fsutil C:\Software command.
Answer: C
Explanation:
To view effective permissions on files and folders Open Windows Explorer, and then locate the file or folder for which you want to view effective permissions. Right-click the file or folder, click Properties, and then click the Security tab. Click Advanced, click the Effective Permissions tab, and then click Select. In Enter the object name to select (examples), enter the name of a user or group, and then click OK. The selected check boxes indicate the effective permissions of the user or group for that file or folder.
QUESTION 407
Hotspot Question
You use a client computer that has Windows 7 Enterprise installed. The computer is located in a branch office. The office is connected by a wide area network (WAN) link to a company’s main office. You need to configure an event subscription that meets the following requirements:
– Forwards events across the WAN on port 3243.
– Forwards events every 6 hours.
– Protects forwarded events while transmission over the WAN network.
What should you do? (To answer, configure the appropriate option or options in the dialog box in the answer area.)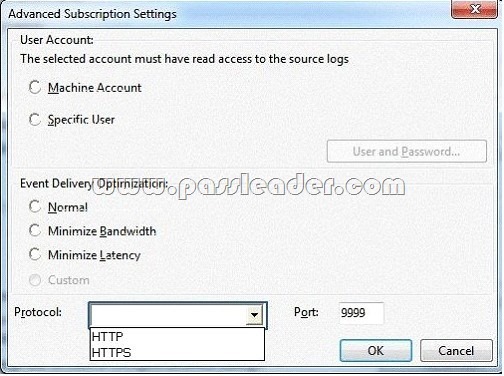
Answer: 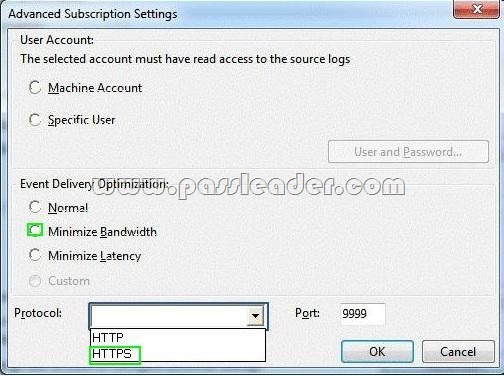
QUESTION 408
Your company has an Active Directory domain and several branch locations. All sales employees use portable computers that have Windows 7 Enterprise installed. Employees report that when they travel to different branch locations, documents that must be printed are sent to printers in their home office. You need to ensure that documents that must be printed are automatically sent to printers at their current locations. What should you do first?
A. Publish all printers to Active Directory.
B. From Devices and Printers, select Change my default printer when I change networks.
C. From Devices and Printers, select the branch office printer, and then select set as default.
D. Configure alternate IP settings.
Answer: B
QUESTION 409
You have a computer that runs a 32-bit version of Windows 7 Home Premium. The computer has a single partition on a single hard disk drive. You want to test a 64-bit version of Windows 7 Ultimate. You configure the computer for a dual boot with previously installed Windows 7 Home Premium. You need to configure the computer to support the dual boot. What should you do?
A. Reinstall Windows 7 Home Premium 32 bit as a 64-bit version.
B. Start Windows 7 Home Premium. Create and mount a new Windows Imaging Format (WIM) file with Windows 7 Ultimate files.
C. Shrink the existing partition and create a new partition to start Windows 7 Ultimate.
D. Install Virtual PC into Windows 7 Home Premium.
Answer: C
Explanation:
Easily Shrink a Volume on a Windows 7 Disk The Windows 7 Disk Management tool provides a simple interface for managing partitions and volumes. There is an easy way to shrink a volume to free up space so you can create a new partition on your disk.
QUESTION 410
You have a computer that runs Windows 7. The computer is a member of a workgroup. You use Encrypting File System (EFS) to protect your local files. You need to ensure that you can decrypt EFS files on the computer if you forget your password. What should you do?
A. From Authorization Manager, modify the Authorization Manager options.
B. Run the cipher.exe /adduser /user:administrator command.
C. From User Accounts, select Manage your file encryption certificates.
D. From Credential Manager, select Back up vault.
Answer: C
http://www.passleader.com/70-680.html
QUESTION 411
You use a desktop computer that has Windows 7 Ultimate SP1. The relevant portions of the computer configuration are shown in the following exhibits: The Disk Management console (Click the Exhibit button.)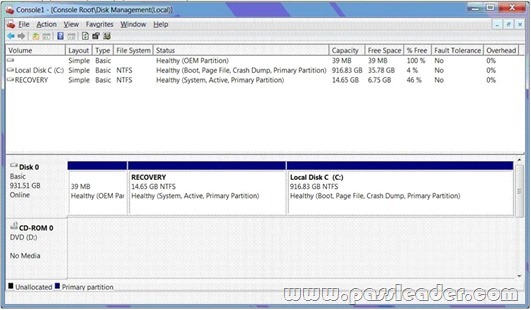
The System Properties window (Click the Exhibit button.)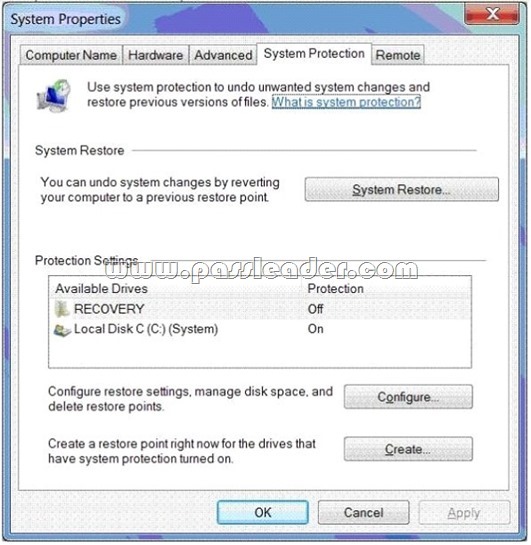
The System protection for Local Disk C window (Click the Exhibit button.)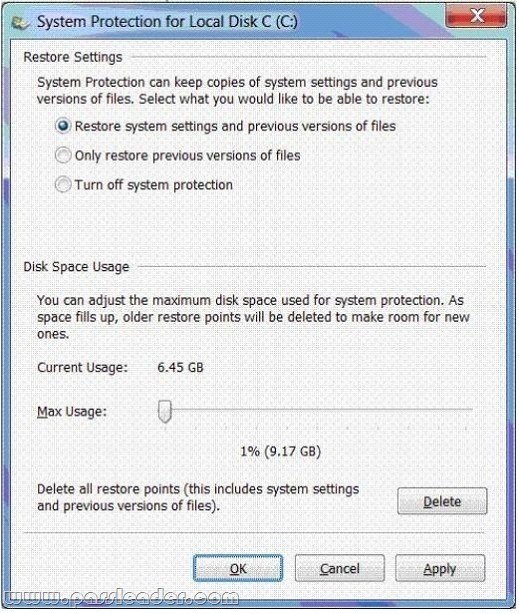
You encrypt several files on an external USB hard disk drive by using the Encrypting File System (EFS). You need to ensure that you can access the files from another computer. What should you do?
A. Delete restore points.
B. Create a restore point.
C. Perform a system restore.
D. Search for the file in the Recycle Bin.
E. Increase disk space used for system protection.
F. Copy the file from a previous version of a folder.
G. Set restore settings to Only restore previous versions of files.
H. Run the cipher /x command from the elevated command prompt,
I. Run the vssadmin list volumes command from the elevated command prompt.
J. Run the vssadmin list shadows command from the elevated command prompt.
K. Run the compact /U <file_name> command from the elevated command prompt.
Answer: H
Explanation:
* cipher /x[:efsfile] [<FileName>]
Backs up the EFS certificate and keys to the specified file name. If used with :efsfile, /x backs up the user’s certificate(s) that were used to encrypt the file. Otherwise, the user’s current EFS certificate and keys are backed up.
* Back Up Your EFS Key
The first time that you use EFS to encrypt something, your system generates a random 256-bit number; that’s the key that EFS uses whenever you encrypt something. To back up your EFS key, simply use the Cipher /x command. Cipher will reply with a message asking if you truly want to back up your EFS key–sadly, I haven’t found a way to suppress this message. Press OK. The tool will then prompt you for the name of the file in which to store the backup. Don’t specify a file extension; Cipher insists on the .pfx extension. For example, if you picked a file named mybackup, you now have a small file called mybackup.pfx. Next, the tool will prompt you to create a password with which to protect that file. Once you’ve got that file created, copy it from your computer’s hard disk to some offline location (e.g., a USB stick, a CD-ROM) and make a note of the password you’ve chosen. Now, in the event of unfortunate circumstances– for example, you lose your profile, you forget your password and a systems administrator has to reset it, the system’s OS fails and you need to recover files directly from the nowdead system’s hard disk–you can simply restore your EFS key by double-clicking the .pfx file and running the resulting wizard. As soon as the wizard is finished, you’ll be able to get to your files again.
QUESTION 412
Hotspot Question
All sales employees use portable computers that have Windows 7 installed. All help desk employees use desktop computers that have Windows 7 installed. You need to ensure that the sales employees are able to request a remote support from a help desk employee when they are in the office. You also need to ensure that sales employees are prevented from receiving remote support during their travel. What should you do? (To answer, configure the appropriate option or options in the dialog box in the answer area.)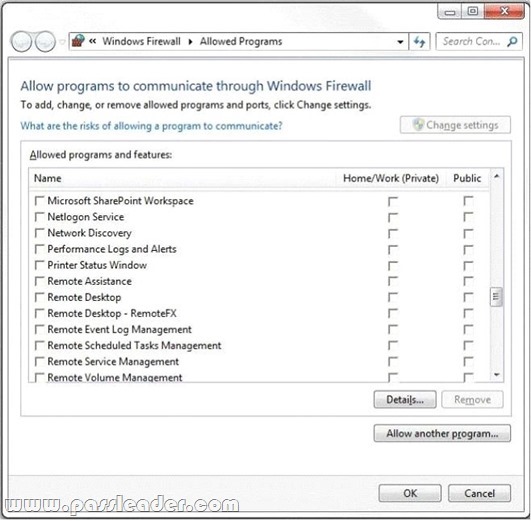
Answer: 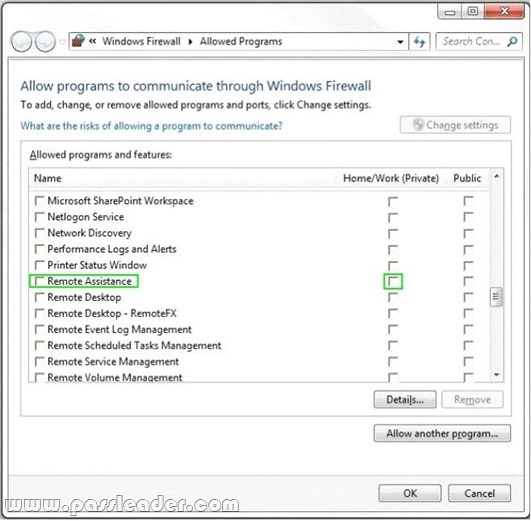
QUESTION 413
Drag and Drop Question
Your organization needs to perform a Windows Vista to Windows 7 migration for a department with 150 computers. You want to use User State Migration Tool (USMT) to automate the migration. You need to move user data and custom settings from the source computers to the destination computers by using USMT with minimal downtime or impact to the end users. The transfer must include files in several custom directories located in the root directory of the boot volume. Which four actions should you perform in sequence? (To answer, move the appropriate four actions from the list of actions to the answer area and arrange them in the correct order. )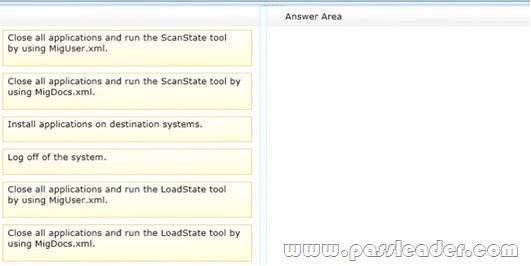
Answer: 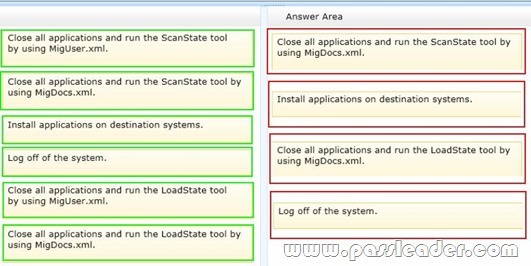
QUESTION 414
You use a computer that has Windows SP1 installed. The computer has a shared folder named c:\Software. User1 is a local user account on the computer. The account is a member of several groups that have access to the C:\Software folders. You need to verify whether User1 can save files to C:\Software. What should you do?
A. Download the Sysinternals Suite bundle from the Microsoft site. Run the AccessEnum tool against the C: \Software folder.
B. Run the Net Share command.
C. Run the Net View command.
D. View the Share permissions on C:\Software.
Answer: D
QUESTION 415
Your company Research department includes client computers that have Windows 7 and Windows Vista installed on separate partitions in a dual-boot configuration. The computers boot into Windows 7 by default or users can choose to boot into Windows Vista during startup. The company management has decided that the Windows Vista partition must be deleted from all the computers. You need to ensure that the staff of the Research department are not prompted to select a boot option during startup and that Windows 7 is chosen automatically. What should you do?
A. In Windows Vista, from an elevated command prompt, run bcdedit /delete {current}.
B. Select the Selective startup option button by using msconfig.exe.
C. In Windows Vista, from an elevated command prompt, run bcdedit /delete {default}.
D. In Windows 7, from an elevated command prompt, run bcdedit /delete {default}.
Answer: A
QUESTION 416
Your laptop has a 400 GB drive and currently reserves, by default, 2% (8 GB) for shadow copies. You need to reserve more space for previous versions of files. What should you do?
A. From System Properties, System Protection, expand the Max usage to 20 GB.
B. From System Properties, System Protection, turn off system protection.
C. From Disk Properties, change the Quota Settings from 8 GB to 20 GB.
D. From System Properties, System Protection, set it to only restore previous versions of files.
Answer: A
QUESTION 417
Drag and Drop Question
You manage the Windows 7 Professional computers for a small architecture firm. All computers operate in workgroup mode. The lead engineer asks you to enable employees to share CAD files located on their desktop computers with all of the other members of the firm. You create a HomeGroup on the lead engineer’s computer. You need to configure the rest of the computers in the firm to join this HomeGroup. Which four actions should you perform in sequence? (To answer, move the appropriate four actions from the list of actions to the answer area and arrange them in the correct order. 1)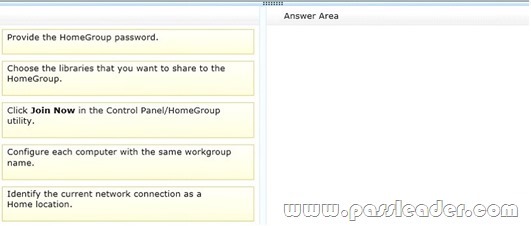
Answer: 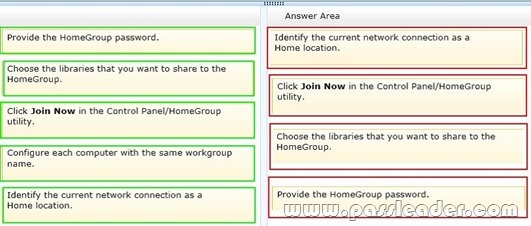
QUESTION 418
You administer client computers that have Windows 7 Enterprise installed. A server names Server1 has an IP address of 10.10.4.46. The server accepts Remote Desktop connections at a custom port 10876. You need to connect to the server from a client computer by using Remote Desktop. What should you do?
A. From an elevated command prompt, run mstsc.exe /v:server1:10876
B. From an elevated command prompt, run msts.exe 10.10.4.56 port:10876
C. From an elevated command prompt, run msts.exe Server1 port:10876
D. From the Advanced tab of your remote Desktop connection, configure the IP address and port of Server1 as the RD Gateway Server
Answer: A
Explanation:
http://windows.microsoft.com/en-us/windows-vista/Use-command-line-parameters-with-Remote-Desktop-Connection
QUESTION 419
You administer computers that have Windows 7 and Internet Explorer 8 installed. You want to log on to one of the computers and access a web-based management application that runs on a server by using Internet Explorer. You need to ensure that any data about your browser session is not saved on the computer. What should you do?
A. From Internet Options, modify the security settings for the Internet zone.
B. From the Local Group Policy, enable the InPrivate Filtering Threshold setting.
C. From Internet Options, select Delete browsing history on exit.
D. From Internet Options, on the Advanced tab, clear Enable DOM Storage.
Answer: C
QUESTION 420
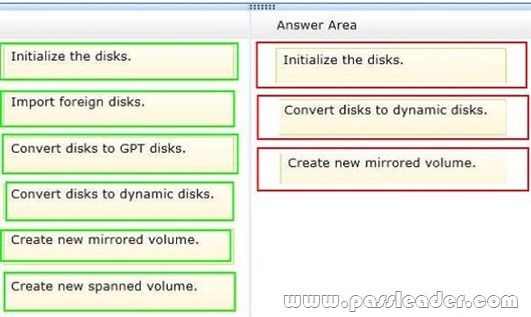
Drag and Drop Question
You use a computer that has Windows 7 Enterprise installed. You install two new hard disk drives and verify that the disks have been detected by Disk Management. You need to configure the two new disks as a software fault-tolerant disk array. What should you do? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.)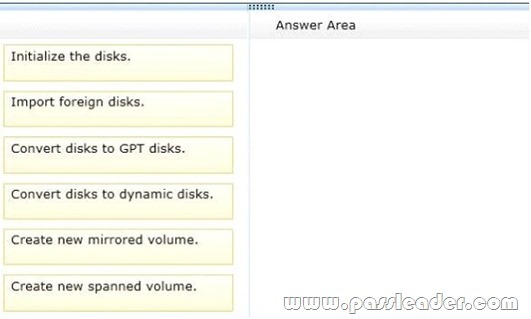
Answer: